General Data Protection Regulation
General Data Protection Regulation (GDPR) Compliance
PERSONAL DATA
Regulation: Your company has a list of all types of personal information it holds, the source of that information, who you share it with, what you do with it and how long you will keep it.
List of all types of personal information LoadOut Pty Ltd holds includes:
- Employee personal data
- Business associates personal data
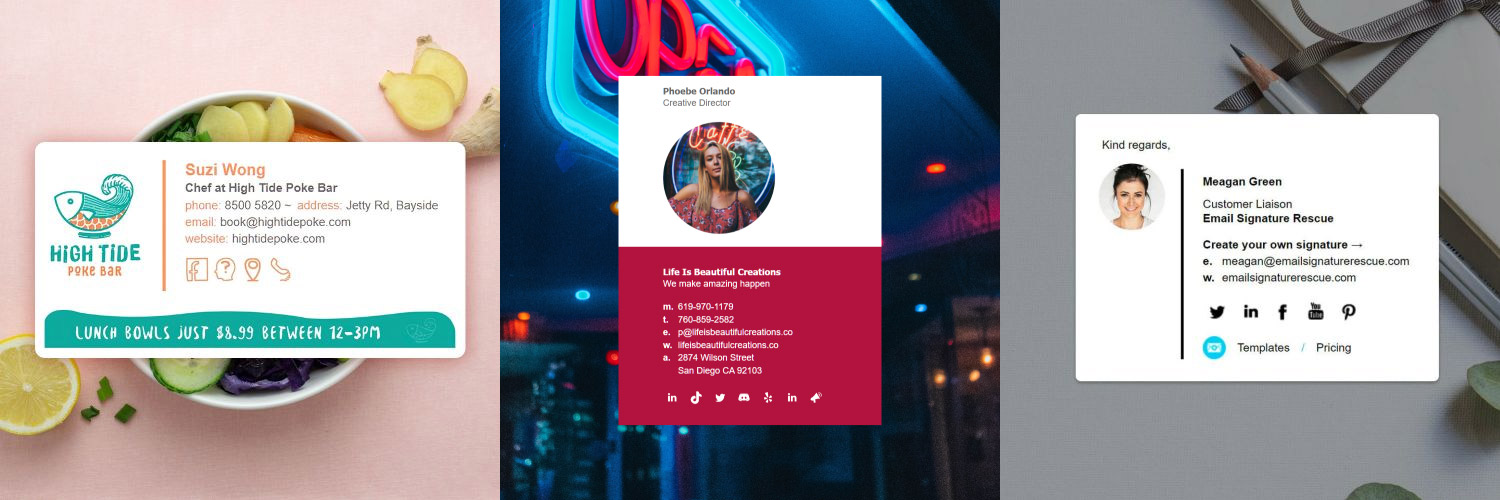
- Users/customers of our online services personal data; including but not limited to Email Signature Rescue (https://emailsignaturerescue.com)
The source of that information comes from users opting in to our services on our websites or hand written forms.
We share this information with third-party services in the every day running of the business including but not limited to:
- Xero (accounting and payroll software)
- Zendesk (help desk and support software)
- Trello (project management software)
- Amazon (web and server hosting services)
- LeadDyno (affiliate marketing software)
- Stripe (payment gateway and billing software)
- Paypal (payment gateway and billing software)
- MaxCDN (content distribution network)
- Google (data processing, marketing, analytics and statistics)
- Atlassian (chat and development tools)
- TeamViewer (remote desktop access software)
- MailChimp (newsletter campaigns and transactional emails)
- Campaign Monitor (newsletter campaigns and transactional emails)
Regulation: Your company has a list of places where it keeps personal information and the ways data flows between them.
Personal data is kept online in third-party software as described above, on a NAS server and on employee computers and laptops. All computers are secured with up to date virus protection (Kaspersky) and have passwords to login. We use a secure business software programs including HipChat, Trello and Skype for data flow. Data flow may also be managed online by users and employees using our services.
Regulation: Your company has a publicly accessible privacy policy that outlines all processes related to personal data.
We have a Privacy Policy.
Regulation: Your privacy policy should include a lawful basis to explain why the company needs to process personal information.
Please see: Information Collection And Use in our Privacy Policy.
Excerpt
While using our Service, we may ask you to provide us with certain personally identifiable information that can be used to contact or identify you and/or your users. Personally identifiable information may include, but is not limited to, email addresses, names, phone numbers, addresses, other information ("Personal Information").
The purpose for which we collect personal information is to provide you with the best service experience possible on the Service and for our internal business purposes that form part of normal business practices. Some provision of personal information is optional. However, if you do not provide us with certain types of personal information, you may be unable to enjoy the full functionality of the Service.
ACCOUNTABILITY & MANAGEMENT
Regulation: Your company has appointed a Data Protection Officer (DPO)
Our DPO is provided at the bottom of this document.
Regulation: Create awareness among decision makers about GDPR guidelines
A meeting took place on the 15th May 2018 with all decision makers in attendance and we thoroughly and thoughtfully discussed the GDPR guidelines and what was required for compliance with our Software Development Team. Those actions are currently taking place and should be implemented by the 25th May 2018.
Regulation: Make sure your technical security is up to date.
Please see our Security & Data Policy
Regulation: Train staff to be aware of data protection
Staff have been informed and provided with information about the GDPR and we have discussed their part in our user's, business associates and other employee's privacy.
Regulation: You have a list of sub-processors and your privacy policy mentions your use of this sub-processor
Please contact us for a list of our Private Contractors if you are a user or employee of any of LoadOut Pty Ltd's services and we will provide them to you confidentially.
Regulation: If your business operates outside the EU, you have appointed a representative within the EU.
To be determined.
Regulation: You report data breaches involving personal data to the local authority and to the people (data subjects) involved
If any data breaches occur we follow a strict protocol:
- Notify all affected data subjects via email.
- Notify the Australian Government, through the Office of the Australia Information Commissioner.
- Work on implementing solutions in our software to ensure that the risk of data breaches in the future are minimized.
- Discuss with employees the risk of data breaches and work on solutions to minimize any risks.
Regulation: There is a contract in place with any data processors that you share data with
We only use legitimate, well-known third-party data processors with their own privacy policies. We ensure that contracts are in place before utilizing any sub-contractors.
NEW RIGHTS
Regulation: Your customers can easily request access to their personal information
Customers can request to access their personal information held on our online software by submitting a support ticket through our website or software.
Regulation: Your customers can easily update their own personal information to keep it accurate
Customers can easily update their own personal information in the software by logging into their account and updating their profiles.
Regulation: You automatically delete data that your business no longer has any use for
When customer information is no longer required for legal or accounting purposes, we delete the data from our software and employee computers. Unless a customer or employee has specifically requested that the information be deleted, the usual time frame for information kept is 7 years from the date that customer or employee left our service.
Regulation: Your customers can easily request deletion of their personal data
Customers can request deletion of their personal data at any time, by submitting a support ticket through our website or software.
Regulation: Your customers can easily request that you stop processing their data
Customers can cancel accounts from within their profile while logged into software or submit a support ticket through our website or software to request that we stop processing their data at any time.
Regulation: Your customers can easily request that their data be delivered to themselves or a 3rd party
Customers can contact support through our website or software and request a copy of all of their held private data in a machine-readable format.
Regulation: Your customers can easily object to profiling or automated decision making that could impact them
Customers can object to profiling or automated decision making by submitting a support ticket through our website or software.
CONSENT
Regulation: Ask consent when you start processing a person's information
We ask for users consent before processing their information. This includes checkboxes on registration pages with information about our privacy policy.
Regulation: Your privacy policy should be written in clear and understandable terms
We believe our privacy policy is easy to read and understand.
Regulation: It should be as easy for your customers to withdraw consent as it was to give it in the first place
Users can withdraw consent by cancelling their account and requesting that their data be deleted through a support ticket on our website or software.
Regulation: If you process children's personal data, verify their age and ask consent from their legal guardian
We do not process children's personal data.
Regulation: When you update your privacy policy, you inform existing customers
When we make changes to our privacy policy, we send an email to all affected users.
FOLLOW-UP
Regulation: You regularly review policies for changes, effectiveness, changes in handling of data and changes to the state of affairs of other countries your data flows to.
We will ensure that we stay up to date with the applicable laws and policy changes of any company that our data flows to.
SPECIAL CASES
Regulation: Your business understands when you must conduct a DPIA for high-risk processing of sensitive data.
We have conducted and will continue to conduct Data Protection Impact Assessments during our planning phase regardless if required, when designing or redesigning our software. We will be proactive in our approach to data privacy.
Regulation: You should only transfer data outside of the EU to countries that offer an appropriate level of protection
We only transfer data outside of the EU to countries that offer an appropriate level of protection such as the United States.
This GDPR Notice (hereinafter referred to as ‘GDPR Notice’) is intended to regulate rights and obligations under the General Data Protection Regulation as of 14 April 2016.
This GDPR Notice describes the use of personal data by the data processor on behalf of its treatment officers, including collection, registration, assembly, storage, extradition or combinations of these.
By registering in the Email Signature Rescue system / application you as a user enters into the user agreement with LoadOut Pty Ltd (the Company) who are responsible for the personal data provided by you and collected according to the purposes stated herein.
All personal data we collect is solely for the purpose of providing the service to you or required to legally run our business. We safely and securely host all data on Amazon US Servers. We use authorized SSL certificates that allow our clients to send and receive data in an encrypted format (HTTPS protocol). This is leading industry practice to prevent MITM attacks and attackers from capturing unencrypted traffic data (like passwords, usernames, or other confidential information).
No critical payment information is stored on our system, such as credit card numbers. All sensitive data is handled directly by our industry leading payment providers, Stripe and PayPal. Connections to our servers are regulated. Although all clients are allowed to upload files to our server, our server configuration prevents the uploading and execution of backdoors or malicious programs.
Our software was built with a focus on security, as such, we are protected from common attacks such as XSS, CSRF and SQL injections. Although we follow industry best practices in regards to secure software development and deployment and backing up data, it is important to note that no system is 100% infallible and we cannot be held liable if confidential information is breached or loss of data occurs.
If your Email Signature Rescue account is cancelled, we continue to securely keep your data. This is purposefully done for the benefit of our users, in paticular for cases where missed payments cause cancellations to occur automatically and users want to reinstate the account by making payment or users choose to re-sign up for the account at a later stage. Should you wish for your account data to be permanently deleted from our service, please email This email address is being protected from spambots. You need JavaScript enabled to view it. and we will delete all account data we hold.
Some private data may also be transferred to third-party software that we use run our business like our accounting software, Xero, our Affiliate Marketing software, LeadDyno, and our Helpdesk software, Zendesk. We only choose to use reputable third-party software providers that have their own clear privacy policies and security/data policies. A full list of software providers we use is provided below.
We may be legally required to keep some of your private data, for example, your company name, address and company business registration ID, for tax purposes. We also keep a record of all correspondence for legal requirements which may include email addresses, names and other personal data that you have submitted to us during your use of our software or when contacting us through our website. In these cases, it's not unreasonable that we do not delete the private data held.
It should be noted that it is the sole responsibility of the user to login and keep their user data up to date. We provide the appropriate tools for users to do so.
Contact Details of the Controller (and controller’s representative if any)
Name of the controller: LoadOut Pty Ltd
Name of the controller representative: Shane Stevens
Address of the controller: PO Box 90, Glenelg, South Australia, Australia 5045
Email of the controller: This email address is being protected from spambots. You need JavaScript enabled to view it.
Phone / Fax of the controller: +61 (08) 8120 0333
Contact Details of the Data Protection Officer (DPO)
Name of the DPO: Shane Stevens
Address of the DPO: PO Box 90, Glenelg, South Australia, Australia 5045
Email of the DPO: This email address is being protected from spambots. You need JavaScript enabled to view it.
Phone / Fax of the DPO: +61 (08) 8120 0333
The purposes of the Processing of the Personal Data
The data provided by the user during registration and as a user of our service is subject to collection, processing, and storage with the purpose to provide the user with the list of services, conducted by the Company, such as:
- Creating, managing and deploying electronic HTML email signatures
- Developing and improving our products and services
- Administration and billing services
- System correspondence such as payment reminders, updates and changes.
- Other Correspondence such as support tickets, emails and newsletters
- Running the day to day operations of the Company
Personal Data Recipients or Categories of Recipients
With the aim of providing services stated above the Company may disclose the personal data collected from the user to such recipients as:
- Stripe
- PayPal
- Amazon Web Services AWS
- LeadDyno
- Xero
- MaxCDN
- Atlassian
- TeamViewer
- MailChimp
- Campaign Monitor
- Zendesk
- Trello
Personal Data Transfer to the Third Parties
Use of subcontractor
If the data processor makes use of a subcontractor or other person who is not normally employed by the data processor, this should be agreed upon in writing with the processing officer before processing personal data.
Agreement with the following subcontractors
- Private Contractors
Anyone who, on behalf of the data processor, performs assignments where the use of the relevant personal information is included shall be familiar with the contractor's contractual and statutory obligations and fulfill the terms thereof.
User Rights
According to the Privacy Policy, the user has the following rights related to the personal data collection and processing:
- right to request from the Association a rectification or erasure of personal data;
- right to restrict personal data processing;
- right to object such personal data processing;
- right to lodge a complaint with a supervisory authority;
- right to withdraw a given consent
- right to request a personal data under processing in a structured format
- right to request to send the data under processing to the third party
Personal Data Storage Period
The criteria that are used to determine a period of data storage. For example, as long as the person is a member / subscriber / contact of the Company or unless he or she required to stop data processing.
User's Consent
Having read the conditions mentioned above the user agrees to the following if they wish to use our application.
I agree that my personal data captured during registration and use of the application will be used by Email Signature Rescue (LoadOut Pty Ltd) for the following purposes:
- To create a user account in the system
- To provide me with a possibility of creating, managing and deploying electronic email signatures for myself and for users and I have the authority to provide such information on their behalf
- To issue and pay my invoices
- To send me the reminders on important events, newsletters, emails with opt-out links included
- To run the day to day operations of the Email Signature Rescue service